| REQUIRED USER ROLE Administrator |
With Single Sign-On (SSO) activated, your users can log into Gladly without the need for a separate username and password. If SSO is already implemented in your company, they can use the same credentials they already use to access other services and applications under the umbrella of your Identity Provider.
Before you start #
Before you activate SSO, we recommend that you first review the following:
- SSO is not required to use Gladly, but we strongly encourage you to use it if you already use SSO internally for access to other apps and services.
- If using SSO, all users are required to use SSO to access Gladly. You can’t have some users on SSO and some that are not.
- It is not allowed to mix different SSO solutions. For example, you can’t use Google SSO and Okta simultaneously.
- Once SSO is activated and properly configured, adding users to Gladly triggers a Gladly user invitation to those users.
- Only upload new users to Gladly once SSO is activated.
Use SSO for Gladly #
- Click
on the top left corner of the screen.
- Click Settings.
- Under the Security and Compliance category, click Single Sign-On.
- Configure the following options from the Single Sign-On page:
- Use SSO – Inactive by default, click the toggle, so it’s green to activate SSO.
- Once SSO is activated, a few more options appear that you’ll need to configure:
- Force users to reauthenticate – Inactive by default, it allows users who log out of Gladly but still have an active SSO session (e.g., Okta, Azure, etc.) to automatically reauthenticate if they access Gladly again. If activated (toggle is green), users must re-authenticate if they log out (excluding closing the Gladly tab or going away) of Gladly.
- Next, set up your identity provider details.
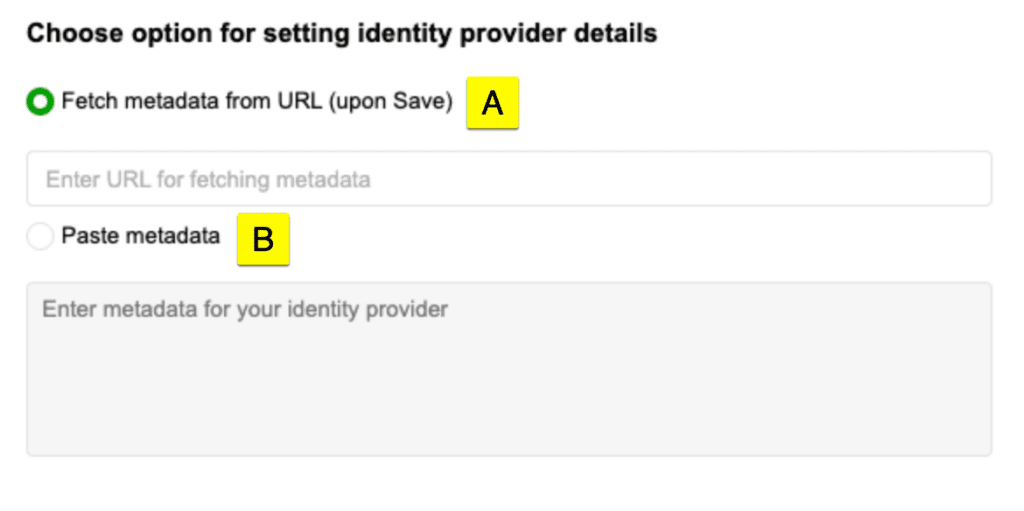
- [A] Fetch metadata from URL (Upon Save) – Found in your SSO provider’s settings, paste the Metadata URL in this field, then click Save. Clicking Save fetches the metadata XML and pastes it in the [B] Metadata field.
- [B] Paste Metadata – This contains the metadata XML fetched from [A] upon clicking Save. For SSO providers like Google Workspace that don’t support metadata URL lookup, you can paste the plain XML file in this field downloaded from the provider.
Generate new metadata #
Gladly automatically fetches metadata using the Fetch metadata from URL link upon clicking Save. If the metadata has changed due to an update (e.g., new SAML certificate), clicking Save automatically fetches the updated metadata.
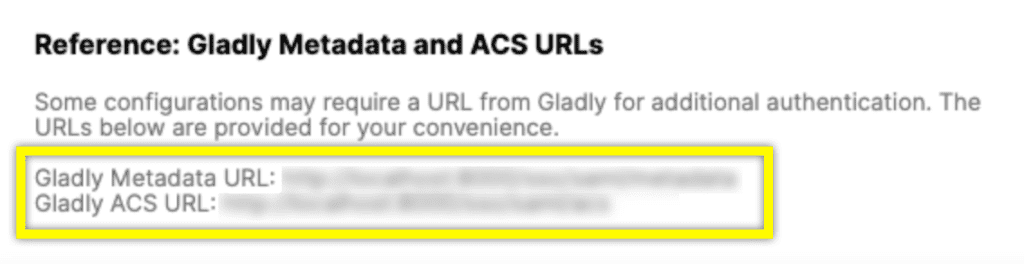
Reference metadata and ACS URL #
Some identity providers like Google Workspace require you to provide the Gladly ACS URL and Entity ID/Meta URL to configure SSO. This information can be found in the bottom section of the Single Sign-On settings page.